Why embedded device security is essential to ICS systems
Protections at the device level are not a replacement for security controls in OT systems and networks. They’re a necessary extension of them. Embedded devices in industrial control systems (ICS) operate within an increasingly complex array of systems, networks and protocols. The complexity is only increasing as end users require more insight into how ICS […]
RBS’s Satellite 2022 Conference quick take on cybersecurity: Increasing urgency, few immediate solutions

The Ukrainian conflict amplified serious questions about satellite security in this year’s conference. But questions aren’t action, which is needed now to protect this critical industry. The Ukrainian conflict amplified serious questions about satellite security in this year’s conference. But questions aren’t action, which is needed now to protect this critical industry. The Ukrainian conflict […]
Adventures of Captain Obvious Issue #24.2
ADVENTURES OF CAPTAIN OBVIOUS ISSUE #24.2 The Cybersecurity Chronicles: Red Balloon Security’s graphic depiction of real-world questions.
Symbiote Injection Process
Multi-step analysis and calibration: How Symbiote integration works RBS’s core technology is highly effective in any embedded device environment, from cars to heavy industry, because it does not require access to source code, or any hardware modifications. On-device security is still controversial. Some industry professionals and manufacturers push back against the very idea of it […]
DHS, Department of Commerce get it right: Firmware security is “overlooked,” — and a genuine cybersecurity risk
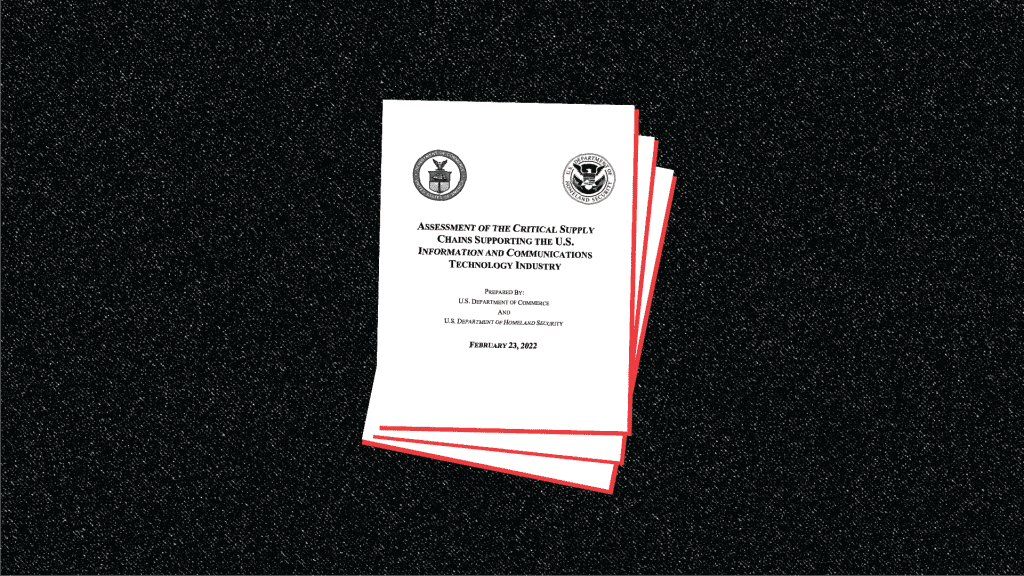
A new report on ICT supply chains helps frame the ongoing threats to the essential code in embedded devices. A new report on ICT supply chains helps frame the ongoing threats to the essential code in embedded devices. A new report on ICT supply chains helps frame the ongoing threats to the essential code in […]
Adventures of Captain Obvious Issue #17.5
ADVENTURES OF CAPTAIN OBVIOUS ISSUE #17.5 The Cybersecurity Chronicles: Red Balloon Security’s graphic depiction of real-world questions.
Shmancybear Funsomware Request
SHMANCYBEAR: A RANSOMWARE PROOF OF CONCEPT Watch this video for a short-take of our ground-breaking research, which was covered in Bloomberg, TechCrunch, ISS Source, Smart Energy International and elsewhere. This is a demonstration that should push embedded devices to the forefront of cybersecurity discussions.
A security assessment of protection relays uncovers cybersecurity weaknesses
The electrical grid depends on protection relays. Our analysis of the hardware and firmware in three models should raise concerns about the state of the industry’s overall security — and safety. Ask any Texan who endured the power outages during a severe winter storm in February 2021 about the critical nature of the electrical grid, […]
Ransomware installation on embedded devices is possible, because we’ve done it
Red Balloon Security’s groundbreaking research has found a means of implementing ransomware on a protection relay. The process is repeatable — and general to embedded devices. Thanks to a spate of high-profile ransomware attacks in recent years, the cyber insecurity of critical infrastructure has lodged in the public consciousness and sparked grave concerns among leaders […]