Introducing RASPUTIN: Automated Hardware Reversing by Red Balloon Security
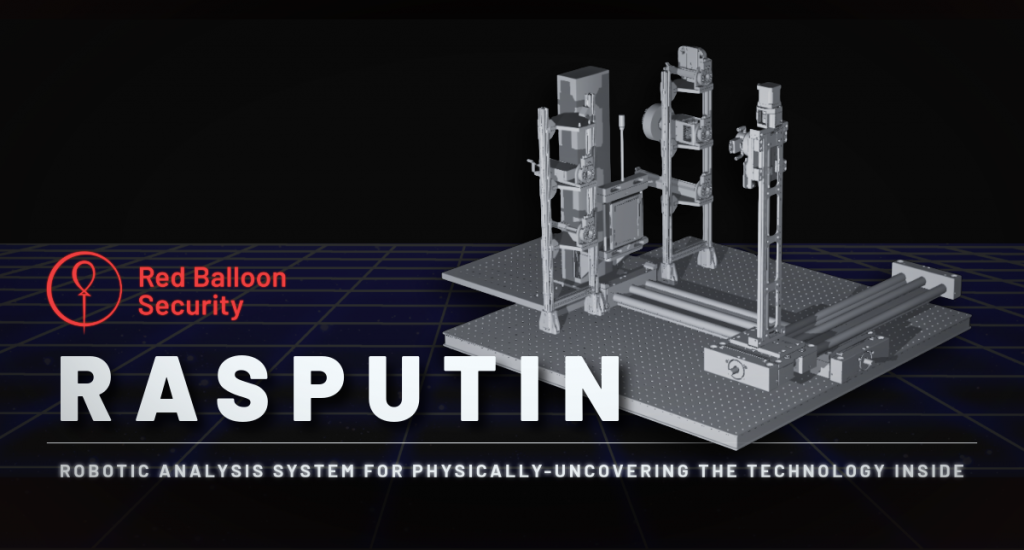
Introducing RASPUTIN: the human-on-the-loop automated hardware reversing platform from Red Balloon Security. Launched in May 2025, RASPUTIN revolutionizes hardware analysis and firmware extraction by combining advanced automation with human oversight.
Hacking Secure Software Update Systems at the DEF CON 32 Car Hacking Village

Read about Red Balloon’s CTF at DEF CON 32’s Car Hacking Village, highlighting secure software updates.
Red Balloon Security Identifies Critical Vulnerability in Kratos NGC-IDU
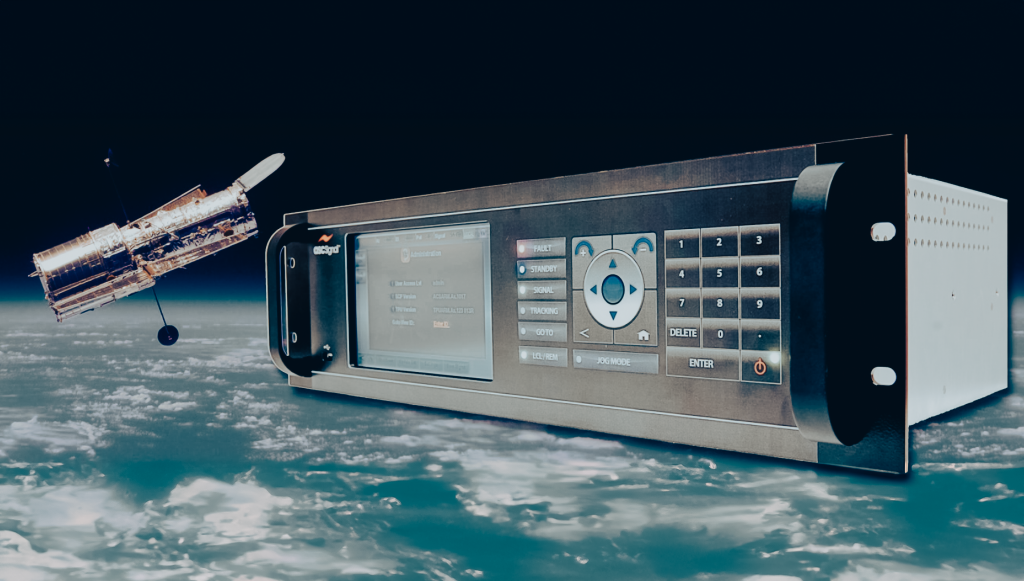
Red Balloon Security Researchers discover and patch vulnerabilities regularly. One such recent discovery is CVE-2023-36670, which affects the Kratos NGC-IDU 9.1.0.4 system. Let’s dive into the details of this security issue.
Hacking In-Vehicle Infotainment Systems with OFRAK 3.2.0 at DEF CON 31
Red Balloon Security attended DEF CON 31 in Las Vegas, Nevada where we contributed two challenges to the Car Hacking Village Capture the Flag (CTF) competition.
Baets by Der

Friendly advice from Red Balloon Security: Just pay the extra $2 Recently, we wanted to use some wired headphones with an iPhone, which sadly lacks a headphone jack. The nearest deli offered a solution: a Lightning-to-headphone jack adapter for only $7. Got to love your local New York City bodega. But a wrinkle appeared: […]
Red Balloon Security Wins 2022 NSF Convergence Accelerator Award for Proposed Improvements to 5G Cybersecurity Through Hardening of Embedded Devices

We’re one of 16 teams chosen to enhance the secure operation of 5G infrastructure. Red Balloon Security has received a $682,000 award from the National Science Foundation’s Convergence Accelerator Program, which includes participation in Phase 1 of the program’s Track G: Securely Operating Through 5G Infrastructure. The Department of Defense is aligned with the NSF […]
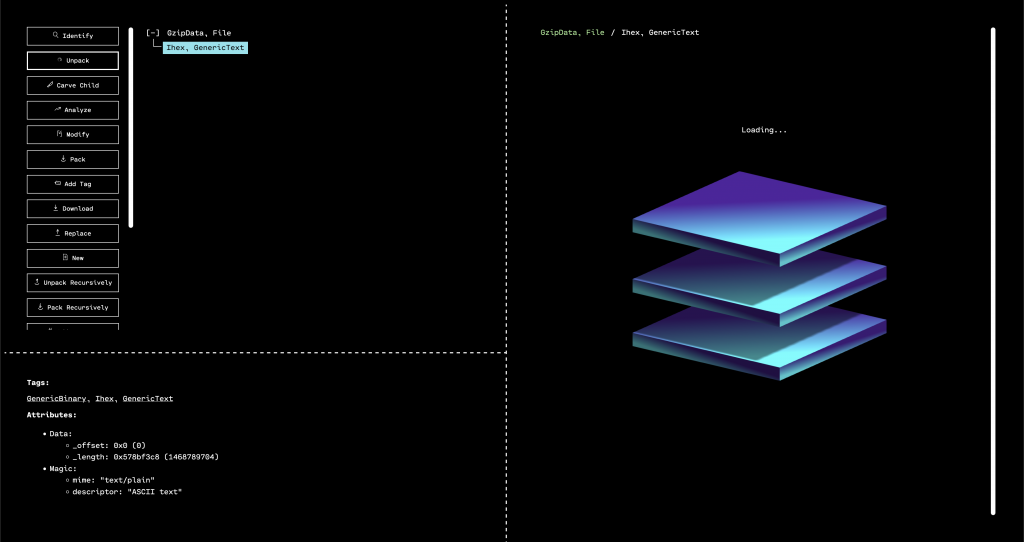
OFRAK: A BOON TO THE CYBER SECURITY COMMUNITY, EMBEDDED DEVICE MANUFACTURERS, AND END USERS, IN 7 QUESTIONS

The release of RBS’s firmware reverse engineering tool is consistent with government and industry calls for higher security standards.
DEF CON 30 Badge Fun with OFRAK
The TL;DR? We used OFRAK to rewrite the badge firmware so that it auto-plays the solution for Challenge 1. Check out our video and full breakdown.
Embedded Systems and Aerospace & Satellite Cybersecurity
Red Balloon Security White Paper Defending From Within: Why Embedded Systems Are the Essential to Achieving Space and Satellite Cybersecurity Table of Contents: Executive Summary State of Cybersecurity in Space and Satellite Systems The Global Landscape 3 Shaping a Safer Future RedBalloonSecurity Investigations CyberLeo 2022 Defend from Within: Symbiote Embedded Defense for […]
ICS-CERT vulnerability analysis
What’s in a vulnerability: Evaluating host-based defense through recent ICS device data We analyzed data from the national vulnerability database to assess the applicability of on-device security features Whether they are discovered by independent researchers, manufacturers, or cyber attackers, device vulnerabilities traditionally have been remedied via patching. Although reactive, patching’s effectiveness is easy enough to […]